Introduction to Cybersecurity Risk Management Supplier
Cybersecurity risk management suppliers are vital in an interconnected world where supply chain breaches impact 98% of organizations. A weak link can trigger a domino effect, jeopardizing data, reputation, and operations. Cyber risks extend beyond data loss, leading to financial drains and operational halts. Collaborating with suppliers to strengthen defenses helps prevent cracks in your cyber strategy.
In this post, let’s learn how to mitigate risks and build resilience through effective cybersecurity risk management partnerships.
Understanding the Supplier Landscape
To effectively manage cybersecurity risks, organizations must clearly understand their supplier relationships and the potential threats they pose.
#1. Mapping the Supply Chain
Organizations must start by mapping their supply chain through a structured and comprehensive approach to manage cyber risks effectively. Key steps include:
- Identify Key Suppliers: Sort suppliers in the catalog according to their importance to the company. A recent survey revealed that over 60% of firms experienced at least one breach caused by third-party vendors. This highlights the importance of evaluating suppliers’ access to sensitive data and systems.
- Visualize Supply Network: Create a flowchart or network diagram to illustrate data flows and interdependencies within the supply chain. This visualization helps identify vulnerabilities and potential failure points that could lead to security breaches.
Organizations can adopt cyber supply chain risk management (C-SCRM) frameworks like NIST’s, which emphasize a risk management approach across supplier relationships to proactively address vulnerabilities and enhance supply chain security.
#2. Assessing Supplier Risk Profiles
Organizations must comprehensively evaluate their suppliers’ security practices and certifications to ensure robust protection against potential threats. Key considerations include:
- Industry-Specific Risks and Regulations: Different industries face unique challenges. For instance, healthcare organizations must comply with strict HIPAA regulations to protect sensitive data. Alarmingly, 90% of healthcare organizations experienced data breaches in 2022, often due to vulnerabilities in third-party services.
- Potential Impact of Breaches: It is crucial to evaluate the likely consequences of supplier-level breaches. For example, if a cloud service provider compromises its system, it could expose sensitive data from all client companies using that service.
Regular assessments are essential to identify weaknesses in suppliers’ security measures and prevent catastrophic breaches. By prioritizing robust security practices, organizations can mitigate vulnerabilities and safeguard data.
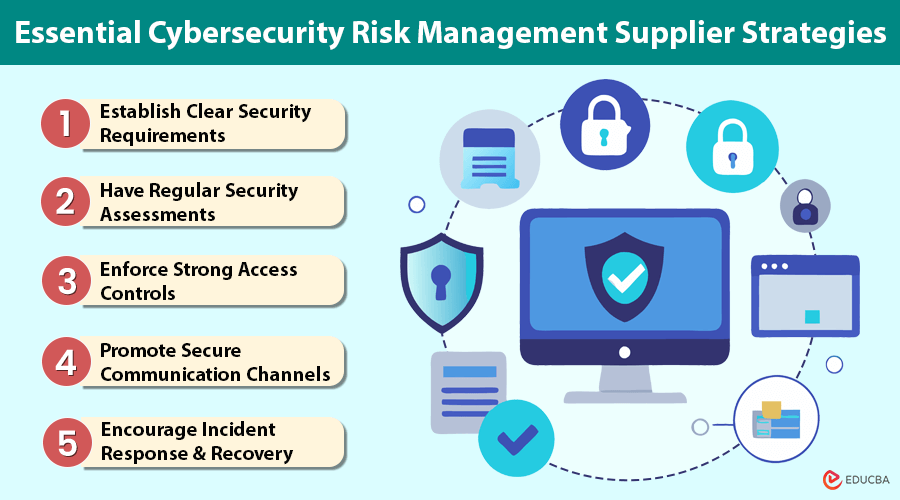
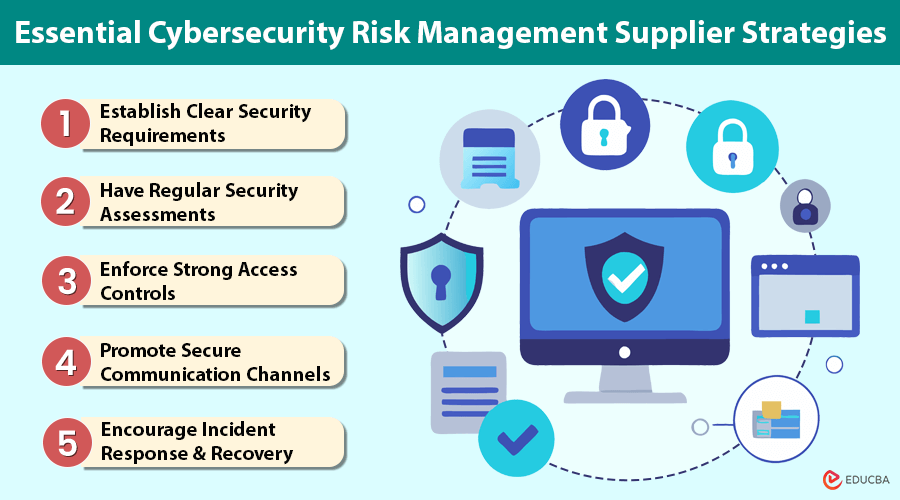
5 Essential Cybersecurity Risk Management Supplier Strategies
To strengthen cybersecurity resilience and safeguard sensitive data, organizations must implement proactive strategies to manage risks related to their suppliers. These measures ensure that suppliers adhere to security standards and minimize potential vulnerabilities.
#1. Establish Clear Security Requirements
To mitigate risks effectively, organizations should:
- Establish Security Standards: Tailored security standards for suppliers should focus on critical areas such as data encryption, access controls, and incident response protocols. For example, requiring suppliers to obtain ISO 27001 certification ensures adherence to internationally recognized information security standards.
- Contractual Security Requirements: Integrate security clauses into supplier contracts to mandate compliance and outline consequences for breaches. View and update these standards regularly to address evolving threats and maintain robust protection.
#2. Have Regular Security Assessments
Periodic security audits and penetration testing of suppliers are crucial for organizations to ensure robust cybersecurity practices.
- Mandating Incident Response: This ensures that the organization and its suppliers are prepared to respond effectively to potential breaches and have clear steps to follow when an incident occurs.
- Ongoing Supplier Monitoring: Organizations can implement real-time monitoring tools to gain visibility into their suppliers’ security postures. This helps identify vulnerabilities early and stay informed about changes in security standards or conditions.
This proactive strategy improves overall cyber resilience and cultivates an accountable culture among suppliers.
#3. Enforce Strong Access Controls
To protect sensitive data, access controls are necessary and ensure adequate protection, organizations should:
- Restrict Access Necessity: Implementing the principle of least privilege ensures that individuals, such as suppliers, only have access to the information necessary for their specific roles.
- Enforce Password Policies: These practices significantly reduce the risk of unauthorized access. A recent survey found that organizations using MFA experienced 50% fewer account compromises than those without.
- Review and Revoke Access: Regular audits of user access rights ensure that former employees or irrelevant personnel do not retain access to sensitive systems.
#4. Promote Secure Communication Channels
When dealing with suppliers, secure communication is crucial to protect sensitive information.
- Implement Encryption Protocols: Utilize encryption protocols such as TLS to ensure data remains confidential during transfers between parties.
- Update Communication Systems: Consistently update communication platforms to prevent vulnerabilities that cybercriminals may exploit.
- Monitor Access and Breaches: Utilize monitoring tools to detect suspicious activities in real-time, enabling quick response to prevent potential data breaches.
#5. Encourage Incident Response & Recovery
Developing joint incident response plans with suppliers is crucial for effective risk management.
- Ongoing Security Awareness Training: Train internal teams and suppliers to recognize potential threats and adopt best practices for threat mitigation.
- Incident Reporting Channels: Set clear protocols for reporting incidents, ensuring timely communication and reducing the impact of breaches.
Building Strong Supplier Relationships
Developing and maintaining strong, collaborative relationships with suppliers ensures effective management of cybersecurity risks.
Organizations can create a secure and resilient supply chain by fostering trust and mutual understanding.
#1. Open and Transparent Communication
Engaging in open dialogue with suppliers about cybersecurity fosters collaboration and strengthens security with the right cybersecurity risk management supplier.
- Establish Regular Communication: Regular meetings or updates allow for discussions on emerging threats or vulnerabilities.
- Encouraging Information Sharing: Creating a comfortable environment for both parties to share risks and concerns enhances security.
#2. Collaborative Risk Management
Organizations should collaborate with suppliers to identify and mitigate risks by:
- Sharing Practices and Lessons: Building solid partnerships helps create more secure supply chain policies through shared knowledge and experiences.
- Conduct Security Exercises: Simulating cyber incidents enables both parties to practice response strategies, ensuring preparedness for real-life situations.
#3. Making Security Performance Incentive
One must integrate security performance into supplier evaluation processes.
- Incentives for Strong Practices: Recognizing and rewarding suppliers with robust cybersecurity measures encourages compliance and fosters continuous improvement.
- Implement Penalties: Establishing clear consequences for failing to meet security standards ensures suppliers remain accountable and committed to maintaining high-security levels.
Final Thoughts
Cybersecurity risk management suppliers are essential for an organization’s cybersecurity framework. As cyber threats evolve, it is crucial to continuously monitor and improve supplier relationships to protect against potential breaches. Supplier security must be a priority, as a company must ensure its partners’ security to safeguard its assets. By applying these strategies, businesses can reduce cybersecurity risks from third-party vendors, strengthening their overall security posture.
Recommended Articles
We hope this article on cybersecurity risk management suppliers has been helpful. For more insights on cybersecurity management topics, check out our other recommended articles.
- Why Choose Cybersecurity?
- Cybersecurity Threats
- Importance of Cybersecurity
- Data Analytics in Cybersecurity
